Tekton Triggers
作者: Ryan 发布于: 4/16/2024 更新于: 7/21/2025 字数: 0 字 阅读: 0 分钟
前面我们都是通过创建一个 TaskRun 或者一个 PipelineRun 对象来触发任务,但是在实际的工作中更多的是开发人员提交代码过后来触发任务,这个时候就需要用到 Tekton 里面的 Triggers 概念了。
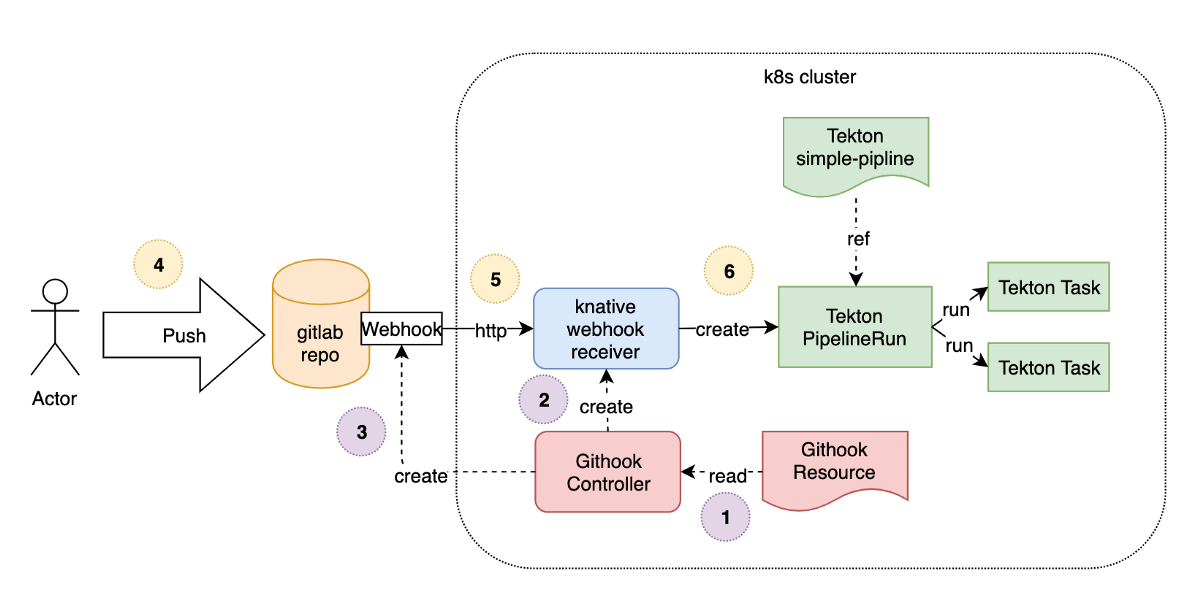
Tekton Triggers 的核心组件
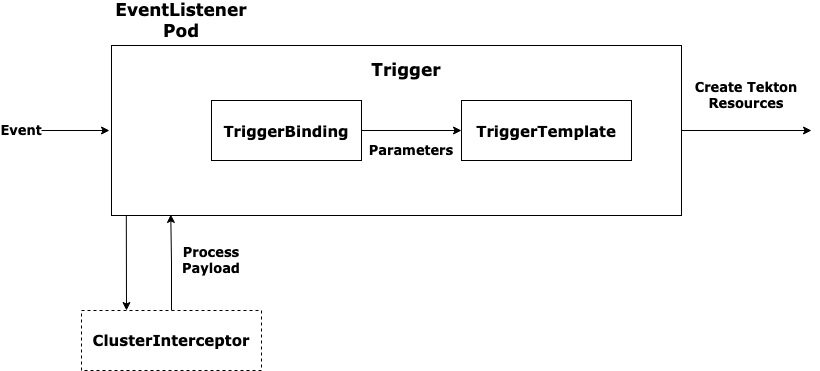
- EventListener:监听来自外部的 HTTP 请求,通常是由 webhook 或其他系统发送的事件。它将接收到的请求数据传递给 TriggerBinding 和 TriggerTemplate。
- TriggerBinding:从接收到的事件数据中提取需要的值。这些值会用来填充 Tekton Pipeline 或 TaskRun 的参数。
- TriggerTemplate:定义如何基于 TriggerBinding 提取的数据生成资源(例如 PipelineRun 或 TaskRun)。
- Interceptor(可选):可以用来对传入的事件做进一步的预处理或验证。例如,GitHub Webhook 事件可以通过 Interceptor 进行验证和筛选。
Tekton Triggers 的典型工作流
- 接收事件:通过
EventListener,Tekton Triggers 接收来自外部系统(如 GitHub、GitLab 或自定义系统)的事件。 - 解析事件:
TriggerBinding提取事件中的重要数据,通常是 JSON 格式的 payload。 - 启动 PipelineRun 或 TaskRun:使用
TriggerTemplate创建PipelineRun或TaskRun,并使用TriggerBinding提取的数据作为参数填充 Pipeline 或 Task。
我们可以使用触发器实现以下 CI/CD 工作流:
- Triggers 监听
git commit或git pull request事件。当检测到时,它会使用提交的代码执行一个单元测试的Pipeline。 - Triggers 监听指示测试成功完成的
git push事件,当它检测到时,它会验证测试的结果并执行构建测试代码的Pipeline。 - 当关联的
PipelineRun执行完成时,Triggers 检查构建的结果,如果成功,则执行一个Task,将构建结果上传到对应的 Docker 镜像仓库。 - 最后,Docker registry 发送一个事件到
Pub/Sub,该事件触发一个将构建镜像推送到 staging 环境的Pipeline。
安装 Triggers
1. 版本选择
Required Kubernetes Version 版本兼容
- Starting from the v0.23.x release of Triggers: Kubernetes version 1.24 or later
- Starting from the v0.22.x release of Triggers: Kubernetes version 1.23 or later
- Starting from the v0.21.x release of Triggers: Kubernetes version 1.22 or later
我们这里集群版本是 1.22.2 选择 安装 0.21 版本
2.安装 Triggers
使用 Tekton Triggers 就需要安装对应的控制器,可以直接通过 tektoncd/triggers 的 GitHub 仓库说明进行安装,如下所示的命令:
kubectl apply -f https://storage.googleapis.com/tekton-releases/triggers/previous/v0.21.0/release.yaml
kubectl apply -f https://storage.googleapis.com/tekton-releases/triggers/previous/v0.21.0/interceptors.yaml
release.yaml文件包含了 Tekton Triggers 的主要组件和资源的定义,是用于部署整个 Tekton Triggers 系统的核心文件。它包括了所有必要的 Kubernetes 资源配置,比如 CRDs(Custom Resource Definitions)、Controller、Webhook、Service Account、Role、RoleBinding 等。
interceptors.yaml文件专门用于安装 Tekton Triggers 中的拦截器(Interceptors)。拦截器是 Tekton Triggers 的一个可选组件,用于在事件触发流程中执行额外的逻辑,比如校验签名、筛选事件、修改请求内容等。
由于国内网络原因gcr.io 镜像要进行替换。
root@docker-proxy:~# docker images | grep tekton | grep v0.21.0
registry.cn-beijing.aliyuncs.com/xxk8s/tekton-interceptors v0.21.0 d390f1b7afb4 54 years ago 79.4MB
registry.cn-beijing.aliyuncs.com/xxk8s/tekton-triggers-webhook v0.21.0 1859abc674cd 54 years ago 81.9MB
registry.cn-beijing.aliyuncs.com/xxk8s/tekton-triggers-eventlistenersink v0.21.0 3250a285cdbf 54 years ago 81.2MB
registry.cn-beijing.aliyuncs.com/xxk8s/tekton-triggers-controller v0.21.0 a50072a0b9e1 54 years ago 83MB3. 检查版本
可以检查 Tekton Triggers 的版本以及确认是否已经包含你想使用的 Interceptor。
使用以下命令查看 Tekton Triggers 版本:
root@master01:/k8s-Examples/kube-ops/tekton# tkn version
Client version: 0.36.0
Pipeline version: v0.37.2
Triggers version: v0.21.0
Dashboard version: v0.37.0可以使用如下命令查看 Triggers 的相关组件安装状态,直到都为 Running 状态:
$ kubectl get pod -n tekton-pipelines
NAME READY STATUS RESTARTS AGE
tekton-dashboard-cdd55dcd-mhf9z 1/1 Running 0 3d1h
tekton-pipelines-controller-5d554db6c-2djkm 1/1 Running 0 3d3h
tekton-pipelines-webhook-578dcd6d5d-b7cnb 1/1 Running 0 3d3h
tekton-triggers-controller-66584b8fdd-7zx6h 1/1 Running 0 2m46s
tekton-triggers-core-interceptors-664497954f-s8qqz 1/1 Running 0 57s
tekton-triggers-webhook-76c44f6f74-j6jn4 1/1 Running 0 2m45s如何结合 Tekton Triggers ?
现在我们来将前面的 Jenkins Pipeline 流水线转换成使用 Tekton 来构建,代码我们已经推送到了私有仓库 GitLab,地址为:http://git.k8s.local/course/devops-demo.git。
要将这个 Pipeline 与 Tekton Triggers 结合,可以按照以下步骤进行设置。
1. 创建 TriggerBinding
TriggerBinding 的主要作用是在接收到事件(如 GitLab 的 webhook)时,提取有用的信息(如仓库地址、提交 ID 等),然后将这些信息作为参数传递给 Tekton Pipeline 或 Task。这个机制可以动态地响应不同的事件,并根据事件内容触发不同的 CI/CD 流程。
在这个例子中,我们从 GitHub 的 push 事件中提取 git-url 和 git-revision:
apiVersion: triggers.tekton.dev/v1beta1
kind: TriggerBinding
metadata:
name: github-pipeline-binding
spec:
params:
- name: git-url
value: "$(body.repository.clone_url)"
- name: git-revision
value: "$(body.ref)" # 例如 'refs/heads/main'
- name: base-version
value: "1.0.0" # 默认版本,可以根据需要修改
- name: image
value: "$(body.repository.name)" # 使用仓库名称作为镜像名称
- name: registry_url
value: "your-registry-url" # 你可以根据需求动态生成或固定
- name: insecure_registry
value: "false" # 示例值
- name: registry_mirror
value: "your-registry-mirror" # 示例值这里需要注意的是参数的值我们是通过读取 GitLab WebHook 发送过来的数据值,通过 $() 包裹的 JSONPath 表达式来提取的,关于表达式的更多用法可以查看官方文档说明,至于能够提取哪些参数值,则可以查看 WebHook 的说明,比如这里我们是 GitLab Webhook 的 Push Hook,对应的请求体数据如下所示:
{
"object_kind": "push",
"before": "95790bf891e76fee5e1747ab589903a6a1f80f22",
"after": "da1560886d4f094c3e6c9ef40349f7d38b5d27d7",
"ref": "refs/heads/master",
"checkout_sha": "da1560886d4f094c3e6c9ef40349f7d38b5d27d7",
"user_id": 4,
"user_name": "John Smith",
"user_username": "jsmith",
"user_email": "john@example.com",
"user_avatar": "https://s.gravatar.com/avatar/d4c74594d841139328695756648b6bd6?s=8://s.gravatar.com/avatar/d4c74594d841139328695756648b6bd6?s=80",
"project_id": 15,
"project": {
"id": 15,
"name": "Diaspora",
"description": "",
"web_url": "http://example.com/mike/diaspora",
"avatar_url": null,
"git_ssh_url": "git@example.com:mike/diaspora.git",
"git_http_url": "http://example.com/mike/diaspora.git",
"namespace": "Mike",
"visibility_level": 0,
"path_with_namespace": "mike/diaspora",
"default_branch": "master",
"homepage": "http://example.com/mike/diaspora",
"url": "git@example.com:mike/diaspora.git",
"ssh_url": "git@example.com:mike/diaspora.git",
"http_url": "http://example.com/mike/diaspora.git"
},
"repository": {
"name": "Diaspora",
"url": "git@example.com:mike/diaspora.git",
"description": "",
"homepage": "http://example.com/mike/diaspora",
"git_http_url": "http://example.com/mike/diaspora.git",
"git_ssh_url": "git@example.com:mike/diaspora.git",
"visibility_level": 0
},
"commits": [
{
"id": "b6568db1bc1dcd7f8b4d5a946b0b91f9dacd7327",
"message": "Update Catalan translation to e38cb41.\n\nSee https://gitlab.com/gitlab-org/gitlab for more information",
"title": "Update Catalan translation to e38cb41.",
"timestamp": "2011-12-12T14:27:31+02:00",
"url": "http://example.com/mike/diaspora/commit/b6568db1bc1dcd7f8b4d5a946b0b91f9dacd7327",
"author": {
"name": "Jordi Mallach",
"email": "jordi@softcatala.org"
},
"added": ["CHANGELOG"],
"modified": ["app/controller/application.rb"],
"removed": []
},
{
"id": "da1560886d4f094c3e6c9ef40349f7d38b5d27d7",
"message": "fixed readme",
"title": "fixed readme",
"timestamp": "2012-01-03T23:36:29+02:00",
"url": "http://example.com/mike/diaspora/commit/da1560886d4f094c3e6c9ef40349f7d38b5d27d7",
"author": {
"name": "GitLab dev user",
"email": "gitlabdev@dv6700.(none)"
},
"added": ["CHANGELOG"],
"modified": ["app/controller/application.rb"],
"removed": []
}
],
"total_commits_count": 4
}2. 创建 TriggerTemplate
请求体中的任何属性都可以提取出来,作为 TriggerBinding 的参数,如果是其他的 Hook 事件,对应的请求体结构可以查看 GitLab 文档说明。
这样我们就可以在 TriggerTemplate 对象中通过参数来读取上面 TriggerBinding 中定义的参数值了,定义一个如下所示的 TriggerTemplate 对象,声明一个 TaskRun 的模板,定义的 Task 任务也非常简单,只需要在容器中打印出代码的目录结构即可:
TriggerTemplate 定义如何根据事件数据生成 PipelineRun。
需要注意在最后的 pipelineresource 中引用参数值的时候使用了一个 tt 的前缀。定义完过后,直接创建上面的资源对象,创建完成后会自动生成 EventListener 的 Pod 和 Service 对象:
apiVersion: triggers.tekton.dev/v1beta1
kind: TriggerTemplate
metadata:
name: pipeline-run-template
spec:
params:
- name: git-url
description: Git repository URL
- name: git-revision
description: Git branch or tag
default: "master"
- name: image
description: Image name
- name: dockerfile-path
description: Path to Dockerfile
default: "Dockerfile"
- name: registry_mirror
description: Registry mirror URL
- name: registry_url
description: Registry URL
- name: insecure_registry
description: Insecure registry URL
- name: base-version
description: Base version for the build
resourcetemplates:
- apiVersion: tekton.dev/v1beta1
kind: PipelineRun
metadata:
generateName: build-and-push-pipeline-run-
spec:
serviceAccountName: build-sa
pipelineRef:
name: build-and-push-pipeline-generate-build-id
workspaces:
- name: git-directory
persistentVolumeClaim:
claimName: git-clone-pvc2
- name: ssh-directory
secret:
secretName: gitlab-ssh-secret
params:
- name: git-url
value: "$(tt.params.git-url)" # 动态传入 git-url
- name: git-revision
value: "$(tt.params.git-revision)" # 动态传入 git-revision
- name: image
value: "$(tt.params.image)" # 动态传入镜像名称
- name: dockerfile-path
value: "$(tt.params.dockerfile-path)" # 动态传入 Dockerfile 路径
- name: registry_mirror
value: "$(tt.params.registry_mirror)" # 动态传入 registry_mirror
- name: registry_url
value: "$(tt.params.registry_url)" # 动态传入 registry_url
- name: insecure_registry
value: "$(tt.params.insecure_registry)" # 动态传入 insecure_registry
- name: base-version
value: "$(tt.params.base-version)" # 动态传入 base-version3. 创建 EventListener
EventListener 监听外部 HTTP 请求,并触发 TriggerTemplate。
我们需要完成触发器的配置,当我们提交源代码到 GitLab 的时候,需要触发 Tekton 的任务运行,所以首先需要完成这个触发器。这里就可以通过 EventListener 这个资源对象来完成,创建一个名为 gitlab-listener 的 EventListener 资源对象,文件内容如下所示:
apiVersion: triggers.tekton.dev/v1beta1
kind: EventListener
metadata:
name: gitlab-listener
spec:
serviceAccountName: tekton-triggers-gitlab-sa # 确保你的 ServiceAccount 有足够权限
triggers:
- name: gitlab-trigger
interceptors: # 添加 GitLab Webhook 拦截器
- ref:
name: gitlab
params:
- name: secretRef # 验证 GitLab Webhook 中的 Secret Token
value:
secretName: gitlab-secret # Kubernetes 中存储的 Secret 名称
secretKey: secretToken # Kubernetes Secret 中的字段名
- name: eventTypes # 限制只处理 Push 事件
value:
- Push Hook
bindings:
- ref: gitlab-pipeline-binding # 绑定到之前创建的 TriggerBinding
template:
ref: pipeline-run-template # 使用我们定义的 TriggerTemplate由于 EventListener 创建完成后会生成一个 Listener 的服务,用来对外暴露用于接收事件响应,比如上面我们创建的对象名为 gitlab-listener,创建完成后会生成一个名为 el-gitlab-listener 的 Service 对象,由于我们 GitLab 本身就在集群内部,所以我们用 Service 的 DNS 形式来访问 EventListener 即可,如果你想暴露到集群外部则可以使用 NodePort 或者 Ingress 的形式。
apiVersion: v1
kind: Service
metadata:
name: gitlab-listener
spec:
type: NodePort # 或者 NodePort,取决于你的 Kubernetes 配置
ports:
- protocol: TCP
port: 8080
targetPort: 8080
nodePort: 31180
selector:
app: gitlab-listener另外需要注意的是在上面的 EventListener 对象中我们添加了 interceptors 属性,其中有一个内置的 gitlab 拦截器,GitLab 拦截器包含验证和过滤来自 GitLab 的请求逻辑, 比如我们可以配置 WebHook 的 Secret Token,可以通过 Secret 对象引入进来:
interceptors:
- ref:
name: gitlab
params:
- name: secretRef # 引用 gitlab-secret 的 Secret 对象中的 secretToken 的值
value:
secretName: gitlab-secret
secretKey: secretToken
- name: eventTypes
value:
- Push Hook # 只接收 GitLab Push 事件对应的 Secret 资源对象如下所示,一个用于 WebHook 的 Secret Token,另外一个是用于 GitLab 登录认证使用的:
apiVersion: v1
kind: Secret
metadata:
name: gitlab-secret
type: Opaque
stringData:
secretToken: '1234567'4567'
---
apiVersion: v1
kind: Secret
metadata:
name: gitlab-auth
annotations:
tekton.dev/git-0: http://git.k8s.local
type: kubernetes.io/basic-auth
stringData:
username: root
password: admin321创建 gitlab 密钥(私钥方式)
kubectl create secret generic gitlab-ssh-secret \
--type=kubernetes.io/ssh-auth \
--from-file=ssh-privatekey=/root/id_rsa_gitlab由于 EventListener 对象需要访问其他资源对象,所以需要声明 RBAC,如下所示:
# event-listener-rbac.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
name: tekton-triggers-gitlab-sa
secrets:
- name: docker-config-secret
- name: gitlab-ssh-secret
- name: git-ssh-secret
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
name: tekton-triggers-gitlab-minimal
rules:
# EventListeners need to be able to fetch all namespaced resources
- apiGroups: ['triggers.tekton.dev']
resources:
['eventlisteners', 'triggerbindings', 'triggertemplates', 'triggers']
verbs: ['get', 'list', 'watch']
- apiGroups: ['']
# configmaps is needed for updating logging config
resources: ['configmaps']
verbs: ['get', 'list', 'watch']
# Permissions to create resources in associated TriggerTemplates
- apiGroups: ['tekton.dev']
resources: ['pipelineruns', 'pipelineresources', 'taskruns']
verbs: ['create']
- apiGroups: ['']
resources: ['serviceaccounts']
verbs: ['impersonate']
- apiGroups: ['policy']
resources: ['podsecuritypolicies']
resourceNames: ['tekton-triggers']
verbs: ['use']
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: tekton-triggers-gitlab-binding
subjects:
- kind: ServiceAccount
name: tekton-triggers-gitlab-sa
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: tekton-triggers-gitlab-minimal
---
kind: ClusterRole
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: tekton-triggers-gitlab-clusterrole
rules:
# EventListeners need to be able to fetch any clustertriggerbindings
- apiGroups: ['triggers.tekton.dev']
resources: ['clustertriggerbindings', 'clusterinterceptors']
verbs: ['get', 'list', 'watch']
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: tekton-triggers-gitlab-clusterbinding
subjects:
- kind: ServiceAccount
name: tekton-triggers-gitlab-sa
namespace: default
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: tekton-triggers-gitlab-clusterrole然后接下来就是最重要的 TriggerBinding 和 TriggerTemplate 对象了,我们在上面的 EventListener 对象中将两个对象组合在一起:
bindings:
- ref: devops-demo-binding # TriggerBinding 对象
template:
ref: devops-demo-template # TriggerTemplate 对象这样就可以将 TriggerBinding 中的参数传递到 TriggerTemplate 对象中进行模板化。比如这里我们定义一个如下所示的 TriggerBinding 对象:
apiVersion: triggers.tekton.dev/v1beta1
kind: TriggerBinding
metadata:
name: devops-demo-binding
spec:
params:
- name: gitrevision
value: $(body.checkout_sha)
- name: gitrepositoryurl
value: $(body.repository.git_http_url)这里需要注意的是参数的值我们是通过读取 GitLab WebHook 发送过来的数据值,通过 $() 包裹的 JSONPath 表达式来提取的,关于表达式的更多用法可以查看官方文档说明,至于能够提取哪些参数值,则可以查看 WebHook 的说明,比如这里我们是 GitLab Webhook 的 Push Hook,对应的请求体数据如下所示:
{
"object_kind": "push",
"before": "95790bf891e76fee5e1747ab589903a6a1f80f22",
"after": "da1560886d4f094c3e6c9ef40349f7d38b5d27d7",
"ref": "refs/heads/master",
"checkout_sha": "da1560886d4f094c3e6c9ef40349f7d38b5d27d7",
"user_id": 4,
"user_name": "John Smith",
"user_username": "jsmith",
"user_email": "john@example.com",
"user_avatar": "https://s.gravatar.com/avatar/d4c74594d841139328695756648b6bd6?s=8://s.gravatar.com/avatar/d4c74594d841139328695756648b6bd6?s=80",
"project_id": 15,
"project": {
"id": 15,
"name": "Diaspora",
"description": "",
"web_url": "http://example.com/mike/diaspora",
"avatar_url": null,
"git_ssh_url": "git@example.com:mike/diaspora.git",
"git_http_url": "http://example.com/mike/diaspora.git",
"namespace": "Mike",
"visibility_level": 0,
"path_with_namespace": "mike/diaspora",
"default_branch": "master",
"homepage": "http://example.com/mike/diaspora",
"url": "git@example.com:mike/diaspora.git",
"ssh_url": "git@example.com:mike/diaspora.git",
"http_url": "http://example.com/mike/diaspora.git"
},
"repository": {
"name": "Diaspora",
"url": "git@example.com:mike/diaspora.git",
"description": "",
"homepage": "http://example.com/mike/diaspora",
"git_http_url": "http://example.com/mike/diaspora.git",
"git_ssh_url": "git@example.com:mike/diaspora.git",
"visibility_level": 0
},
"commits": [
{
"id": "b6568db1bc1dcd7f8b4d5a946b0b91f9dacd7327",
"message": "Update Catalan translation to e38cb41.\n\nSee https://gitlab.com/gitlab-org/gitlab for more information",
"title": "Update Catalan translation to e38cb41.",
"timestamp": "2011-12-12T14:27:31+02:00",
"url": "http://example.com/mike/diaspora/commit/b6568db1bc1dcd7f8b4d5a946b0b91f9dacd7327",
"author": {
"name": "Jordi Mallach",
"email": "jordi@softcatala.org"
},
"added": ["CHANGELOG"],
"modified": ["app/controller/application.rb"],
"removed": []
},
{
"id": "da1560886d4f094c3e6c9ef40349f7d38b5d27d7",
"message": "fixed readme",
"title": "fixed readme",
"timestamp": "2012-01-03T23:36:29+02:00",
"url": "http://example.com/mike/diaspora/commit/da1560886d4f094c3e6c9ef40349f7d38b5d27d7",
"author": {
"name": "GitLab dev user",
"email": "gitlabdev@dv6700.(none)"
},
"added": ["CHANGELOG"],
"modified": ["app/controller/application.rb"],
"removed": []
}
],
"total_commits_count": 4
}请求体中的任何属性都可以提取出来,作为 TriggerBinding 的参数,如果是其他的 Hook 事件,对应的请求体结构可以查看 GitLab 文档说明。
在 Tekton Triggers 中,以下 Interceptors 是内置的,你无需额外安装:
- GitLab Interceptor:用于接收和处理 GitLab Webhook 事件。
例如:
Push Hook、Merge Request Hook等。验证请求中的
X-Gitlab-Token,确保请求的合法性。例如:
push、pull_request等事件。验证 GitHub 的
X-Hub-Signature请求头。
- CEL Interceptor(Common Expression Language):
- 可以用来编写表达式,用于过滤或修改 Webhook 事件的数据。
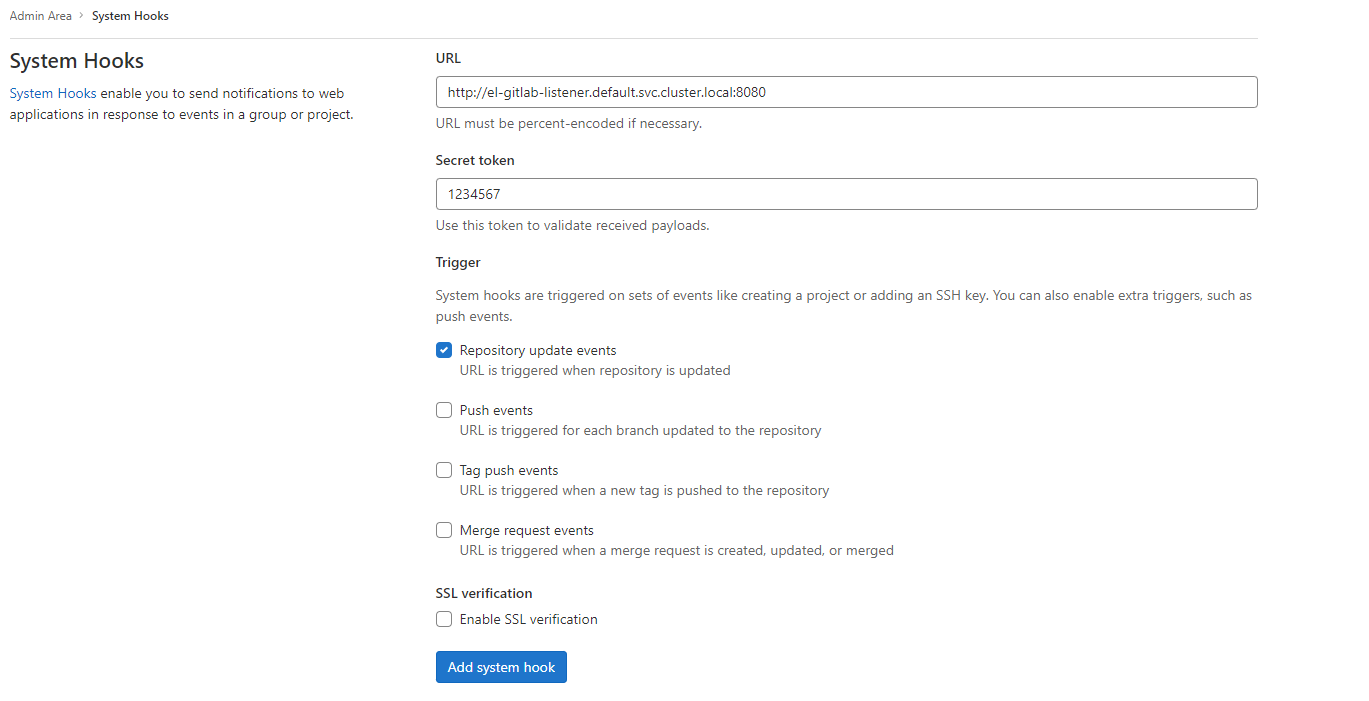
4. 暴露 EventListener
使用 Kubernetes Service 或 Ingress 来暴露 EventListener 的服务,以接收来自 GitHub 等系统的 webhook。
apiVersion: v1
kind: Service
metadata:
name: github-pipeline-listener
spec:
type: LoadBalancer # 或者 NodePort/ClusterIP
ports:
- protocol: TCP
port: 8080
targetPort: 8080
selector:
app: github-pipeline-listener5. 设置 GitHub Webhook
在 GitHub 仓库中,设置 Webhook,将事件发送到 Tekton 的 EventListener 服务。通常,URL 形式如下:
http://<your-service-ip>:8080由于 EventListener 对象需要访问其他资源对象,所以需要声明 RBAC,如下所示:
# event-listener-rbac.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
name: tekton-triggers-gitlab-sa
secrets:
- name: docker-config-secret
- name: gitlab-ssh-secret
- name: git-ssh-secret
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
name: tekton-triggers-gitlab-minimal
rules:
# EventListeners need to be able to fetch all namespaced resources
- apiGroups: ['triggers.tekton.dev']
resources:
['eventlisteners', 'triggerbindings', 'triggertemplates', 'triggers']
verbs: ['get', 'list', 'watch']
- apiGroups: ['']
# configmaps is needed for updating logging config
resources: ['configmaps']
verbs: ['get', 'list', 'watch']
# Permissions to create resources in associated TriggerTemplates
- apiGroups: ['tekton.dev']
resources: ['pipelineruns', 'pipelineresources', 'taskruns']
verbs: ['create']
- apiGroups: ['']
resources: ['serviceaccounts']
verbs: ['impersonate']
- apiGroups: ['policy']
resources: ['podsecuritypolicies']
resourceNames: ['tekton-triggers']
verbs: ['use']
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: tekton-triggers-gitlab-binding
subjects:
- kind: ServiceAccount
name: tekton-triggers-gitlab-sa
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: tekton-triggers-gitlab-minimal
---
kind: ClusterRole
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: tekton-triggers-gitlab-clusterrole
rules:
# EventListeners need to be able to fetch any clustertriggerbindings
- apiGroups: ['triggers.tekton.dev']
resources: ['clustertriggerbindings', 'clusterinterceptors']
verbs: ['get', 'list', 'watch']
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: tekton-triggers-gitlab-clusterbinding
subjects:
- kind: ServiceAccount
name: tekton-triggers-gitlab-sa
namespace: default
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: tekton-triggers-gitlab-clusterrole执行
root@master01:/k8s-Examples/kube-ops/tekton# kubectl apply -f ./triggers/1.test-TriggerBinding.yaml
triggerbinding.triggers.tekton.dev/gitlab-pipeline-binding created
root@master01:/k8s-Examples/kube-ops/tekton# kubectl apply -f ./triggers/2.test-TriggerTemplate.yaml
triggertemplate.triggers.tekton.dev/pipeline-run-template created
root@master01:/k8s-Examples/kube-ops/tekton# kubectl apply -f ./triggers/3.test-EventListener.yaml
eventlistener.triggers.tekton.dev/gitlab-listener created
root@master01:/k8s-Examples/kube-ops/tekton# kubectl apply -f ./triggers/4.test-EventListener-Service.yaml
root@master01:/k8s-Examples/kube-ops/tekton# kubectl apply -f ./triggers/4.test-EventListener-Service.yaml
service/gitlab-listener created
root@master01:/k8s-Examples/kube-ops/tekton#
root@master01:/k8s-Examples/kube-ops/tekton# kubectl get svc
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
el-gitlab-listener ClusterIP 10.100.216.40 <none> 8080/TCP,9000/TCP 28s
gitlab-listener NodePort 10.104.142.166 <none> 8080:31180/TCP 5s
kubernetes ClusterIP 10.96.0.1 <none> 443/TCP 24d
nexus ClusterIP 10.99.196.220 <none> 8081/TCP 16d
root@master01:/k8s-Examples/kube-ops/tekton#接下来我们就可以到 GitLab 的项目中配置 WebHook,注意需要配置 Secret Token,我们在上面的 Secret 对象中声明过:
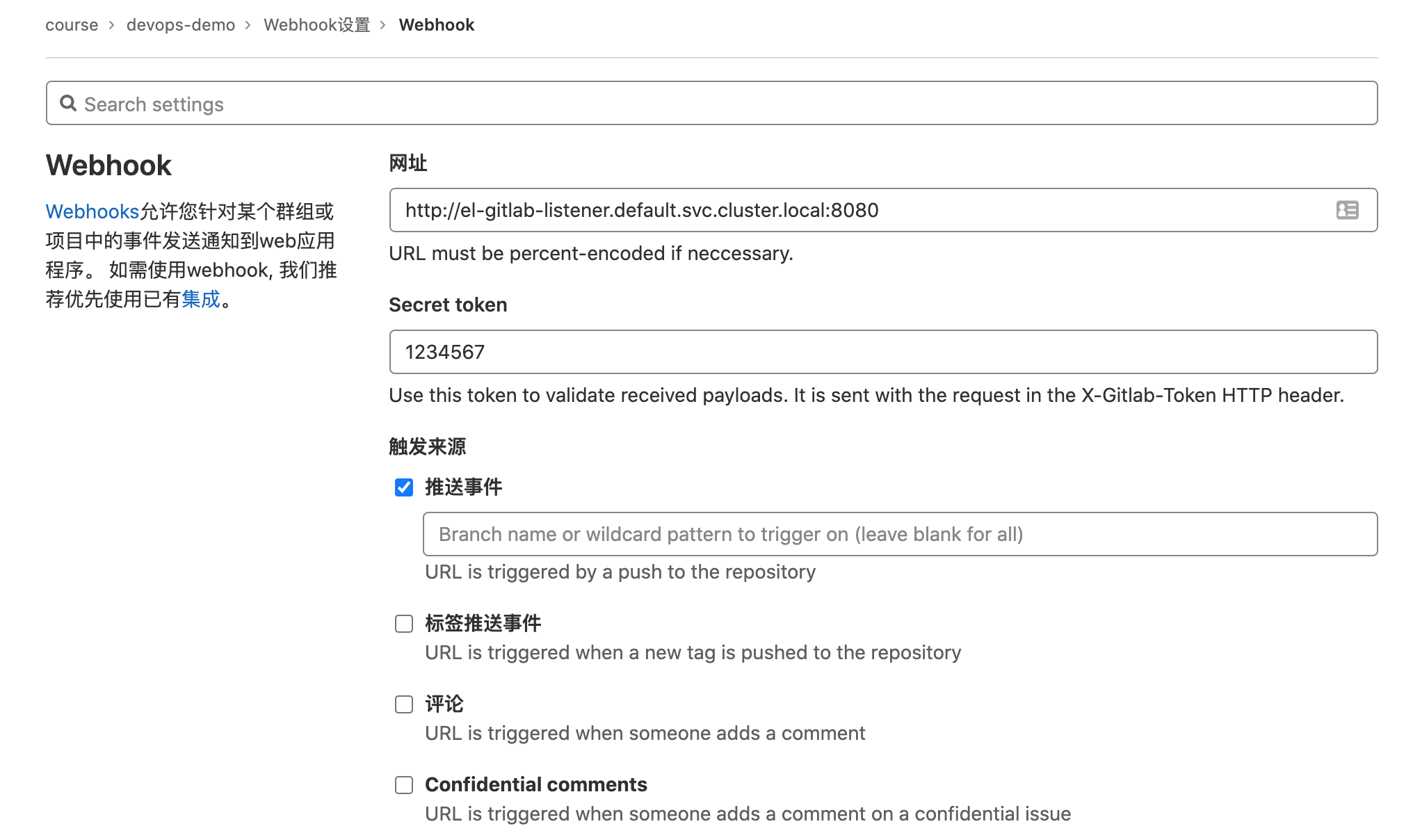
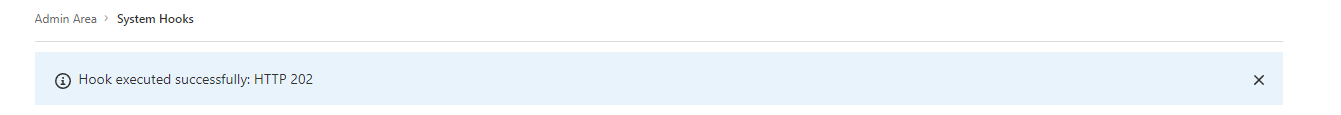
创建完成后,我们可以测试下该 WebHook 的 Push events 事件,直接点击测试即可(如果使用自定义的域名则需要在 coredns 中添加映射),正常会返回 Hook executed successfully: HTTP 202 的提示信息,这个时候在 Kubernetes 集群中就会出现如下所示的任务 Pod:
root@master01:/k8s-Examples/kube-ops/tekton# kubectl get pod -l eventlistener=gitlab-listener
NAME READY STATUS RESTARTS AGE
el-gitlab-listener-cdb79d789-x6bb2 1/1 Running 0 98s创建完成后,我们可以测试下该 WebHook 的 Push events 事件,直接点击测试即可(如果使用自定义的域名则需要在 coredns 中添加映射),正常会返回 Hook executed successfully: HTTP 202 的提示信息,这个时候在 Kubernetes 集群中就会出现如下所示的任务 Pod:
root@master01:/k8s-Examples/kube-ops/tekton# kubectl get eventlistener
NAME ADDRESS AVAILABLE REASON READY REASON
gitlab-listener http://el-gitlab-listener.default.svc.cluster.local:8080 True MinimumReplicasAvailable True
root@master01:/k8s-Examples/kube-ops/tekton# kubectl get eventlisteners.triggers.tekton.dev
NAME ADDRESS AVAILABLE REASON READY REASON
gitlab-listener http://el-gitlab-listener.default.svc.cluster.local:8080 True MinimumReplicasAvailable True查看WebHook 的 Push events 事件日志信息。
kubectl logs el-gitlab-listener-cdb79d789-x6bb2 -f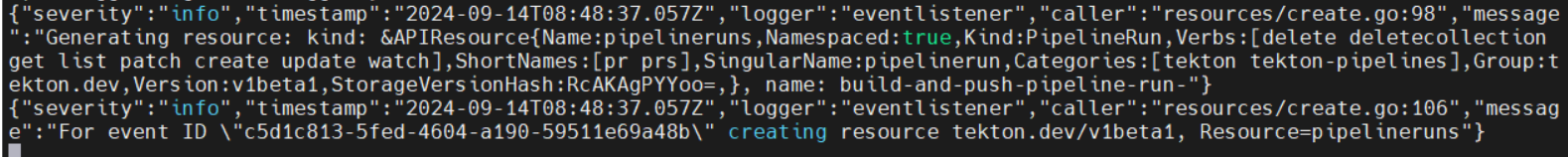
到这里我们就完成了通过 GitLab 的 Push 事件来触发 Tekton 的一个任务。
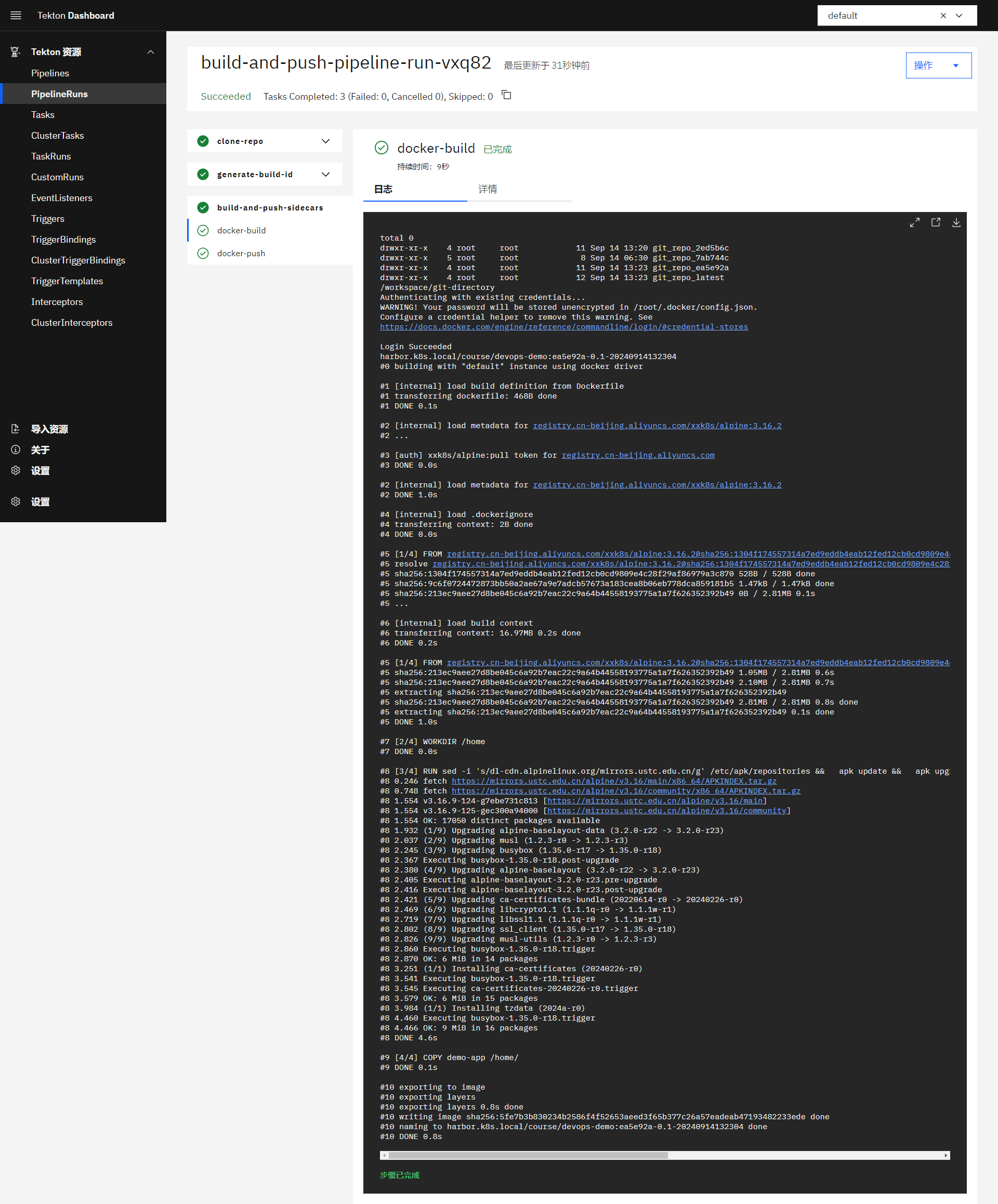
已经看到镜像已经上传到 harbor 中

接下来我们再来实现将我们的应用通过 Tekton 来自动部署到 Kubernetes 集群中。
